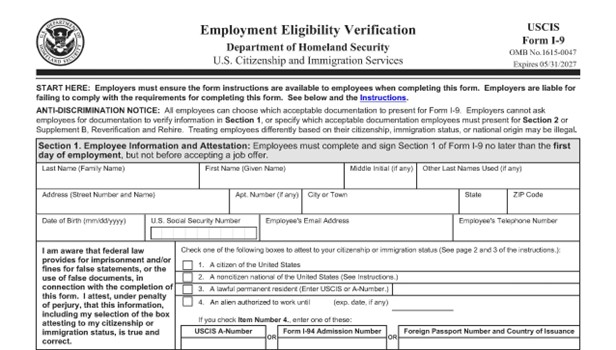
A HIPAA violation occurs when PHI data that identifies an individual and relates to their health status, treatment, or payment is improperly accessed, used, or disclosed. When it comes to patient privacy, ignorance isn’t bliss… it’s expensive. Every healthcare provider, business associate, and third-party vendor that handles protected health information (PHI) is required by law to comply with the Health Insurance Portability and Accountability Act (HIPAA). Yet, year after year, the U.S. Department of Health and Human Services (HHS) Office for Civil Rights (OCR) continues to issue fines for HIPAA violations that can be avoided with proper policies, training, and security safeguards. Even small practices face enforcement actions for these violations, and “I didn’t know” is not a valid defense under HIPAA.
Common HIPAA violations include:
- Sending PHI to the wrong recipient
- Failing to encrypt emails or devices that store ePHI
- Losing laptops, smartphones, or USB drives containing patient data
- Discussing patient details in public areas
- Sharing login credentials or failing to log off workstations
- Posting patient photos or information on social media without authorization
- Not performing an annual risk analysis or updating policies and procedures
Financial and Legal Risks
HIPAA penalties are tiered based on the level of negligence and can range from $141 to over $71,000 per violation — with an annual maximum of $2 million per identical provision (as adjusted for inflation in 2025). OCR considers factors such as the organization’s size, history of compliance, and willingness to correct the issue when determining penalties.
Beyond monetary fines, violations can lead to:
- Civil lawsuits: Patients can sue under state privacy laws.
- Corrective action plans: Mandatory, multi-year compliance monitoring by HHS.
- Reputation damage: Lost patient trust and public exposure of the breach.
- Criminal charges: Willful misuse of PHI can lead to imprisonment.
Operational and Reputational Risks
The real cost of a HIPAA violation goes beyond fines. Breaches disrupt operations, divert staff resources, and erode the confidence of patients and business partners. Once trust is lost, it’s difficult — and expensive — to rebuild.
For example, when a ransomware attack locks down medical records, patient care slows, billing stops, and the organization may spend months recovering. Even worse, news of the breach spreads fast, often drawing negative attention from both patients and regulators.
How to Avoid HIPAA Violations
The best defense is a proactive compliance program. Every covered entity and business associate should:
- Conduct an annual risk analysis to identify and mitigate vulnerabilities.
- Implement and maintain written policies and procedures that align with the Privacy, Security, and Breach Notification Rules.
- Train employees annually and document completion.
- Secure all devices and networks — use encryption, strong passwords, and access controls.
- Review business associate agreements (BAAs) to ensure vendors are also compliant.
- Document everything — if it’s not documented, it didn’t happen.
Protect Your Organization Before It’s Too Late
HIPAA compliance isn’t a one-time project — it’s an ongoing process. At Aris Medical Solutions, our HIPAA Keeper™ system simplifies compliance with a cloud-based platform that walks you through each requirement, step by step. From risk analysis to training and documentation, you’ll have everything you need to stay protected, compliant, and audit-ready.
Protect your practice — and your patients.
Schedule a free HIPAA checkup today at Aris Medical Solutions. Your HIPAA Compliance Officer will have a HIPAA security analyst to guide and assist them every step of the way.